You walk out to your driveway in the morning, ready to head to work. Your keys are still in your pocket. But your car is gone.
No shattered glass. No alarm. No obvious signs of forced entry.
For many drivers, that sounds impossible. But for thieves targeting vehicles with keyless entry systems, it is entirely realistic. In some cases, they do not need to steal your keys at all. They only need to capture and relay the signal your key fob is already broadcasting.
At Argus Cybersecurity and Support, the focus is usually on protecting digital access: passwords, multi-factor authentication, device security, and the systems businesses rely on every day. But the principle is the same here. Whether the target is a Microsoft 365 account or a vehicle in your driveway, attackers look for the easiest path to impersonate a trusted credential and gain access. A relay attack is that same problem applied to your car.
What Is a Relay Attack?
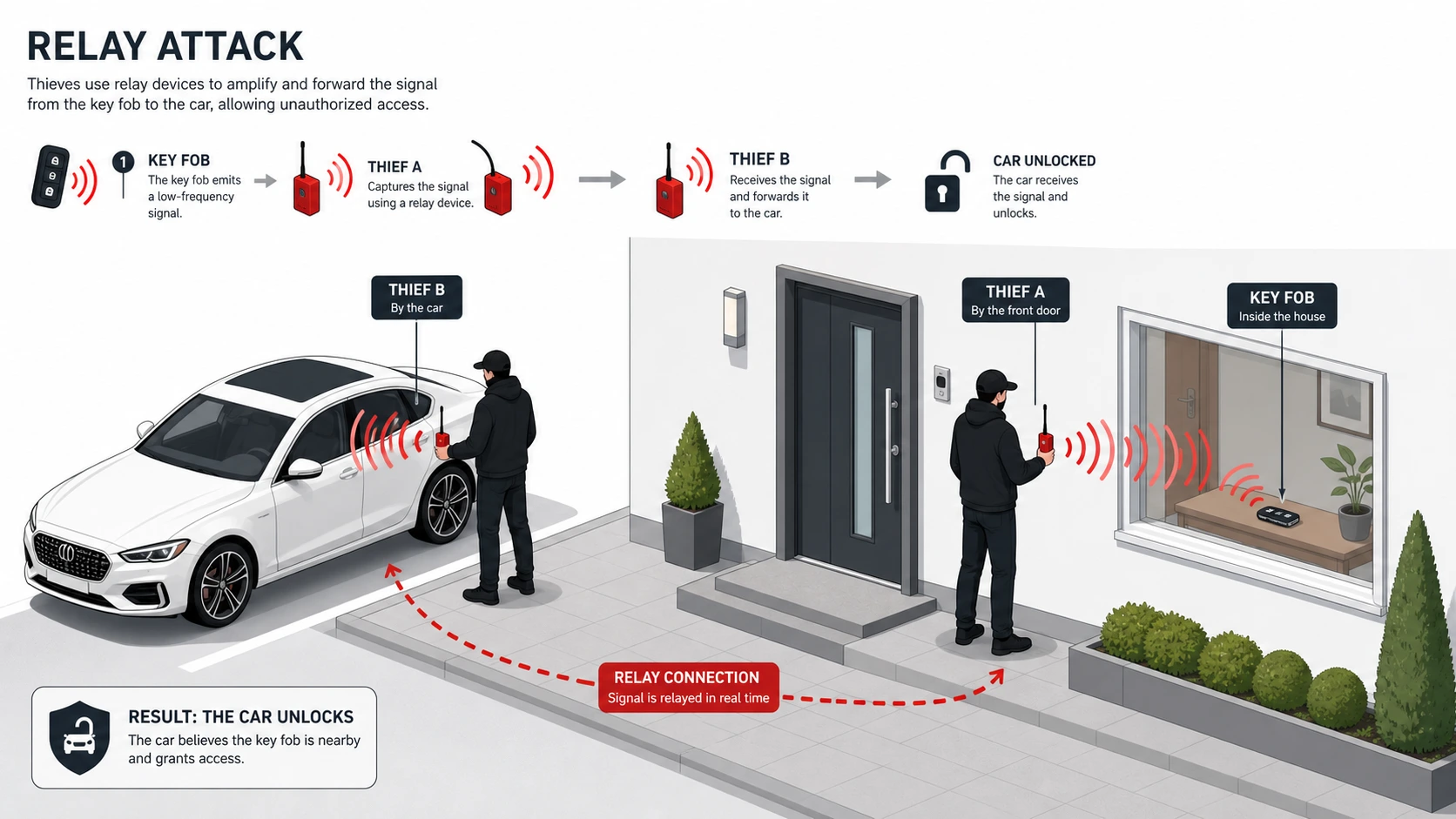
A relay attack is a method thieves use to trick a vehicle into believing its legitimate key fob is nearby, even when the key is still inside your home or office.
Many modern vehicles use passive keyless entry and start systems. These systems are designed to unlock and start the car when the authorized key fob is within range. That convenience is useful, but it also expands the attack surface.
In a relay attack, criminals use electronic devices to capture the signal from your key fob and extend it across a greater distance. The car receives that relayed signal, assumes the real key is close enough to authorize access, unlocks the doors, and may allow the engine to start.

Thief standing outside a door with the relay device in his hand
How the Attack Works
Most relay attacks involve two people and two devices. One thief stands near the house, office entrance, or wherever the key fob is likely to be stored. The second thief stands near the vehicle.
The first device listens for the low-power radio signal coming from the key. The second device receives and retransmits that signal to the car. From the vehicle’s perspective, the signal appears valid, so the vehicle responds as if the real key is nearby.
That is what makes this type of theft so effective. There may be no broken windows, no visible tampering, and no noise to alert anyone nearby.
Why It Matters for Business Owners
For a business owner, the cost of vehicle theft is not limited to the vehicle itself. A stolen van, truck, or employee vehicle can create immediate operational disruption.
Missed appointments, delayed deliveries, lost tools, exposed laptops, paperwork, access badges, and emergency credential resets can all follow a single theft. What begins as a physical security problem can quickly become a broader business continuity and information security issue.
This is where security teams and business owners need to think beyond replacement value. A stolen vehicle can trigger downtime, customer impact, insurance complications, and potential exposure of company assets stored inside.
How to Reduce the Risk
The best defense is layered security. No single control is perfect, but stacking simple protections together makes your vehicle a much less attractive target.
1. Use a Faraday pouch or box
A Faraday pouch or signal-blocking box helps prevent the key fob’s radio signal from being captured. If the signal never leaves the pouch, it cannot be relayed to the car.
This is one of the easiest first steps for most households and businesses. Test it periodically, because low-cost pouches can wear out over time.
2. Keep keys away from doors and windows
Do not leave keys on a hook by the front door, in a bowl near a window, or close to the garage entry. Those locations make it easier for attackers to capture the signal from outside.
Store keys deeper inside the building and farther from exterior walls when possible. Even a modest increase in distance can make signal capture more difficult.
3. Enable extra vehicle-side protections
Some vehicles offer built-in features such as PIN-to-Drive or configurable keyless entry settings. These controls add another barrier, even if the car is unlocked.
If your vehicle supports additional authentication, immobilizer controls, or the ability to reduce passive entry behavior, those settings are worth enabling.
4. Add a visible physical deterrent
A steering wheel lock may seem old-fashioned, but it changes the attacker’s risk calculation. Relay theft depends on speed, and visible deterrents introduce friction, delay, and the possibility of getting caught.
That does not make the vehicle impossible to steal. It makes it less convenient than the next available target.
5. Review whether passive keyless entry can be disabled
Some vehicles and some key fobs allow owners to disable proximity-based unlocking. That means the car will respond only when the fob button is physically pressed.
This will not be the right choice for every driver, but it is worth checking the manual or manufacturer settings. Reducing automatic trust is often a smart security decision.
The Security Takeaway
Convenience and security are often in tension. Keyless systems reduce friction for legitimate users, but they also create new opportunities for attackers who know how to abuse trusted signals.
That is why the right response is not fear. It is layered defense. A signal-blocking pouch, better key placement, a visible lock, and any available vehicle-side authentication features together make theft slower, noisier, and less likely to succeed.
At Argus, that mindset applies everywhere: email, identity, devices, networks, and physical assets. Attackers succeed when systems trust the wrong person, the wrong device, or the wrong signal. The tools may change, but the principle stays the same.
Frequently Asked Questions:
Not every keyless vehicle is equally vulnerable, but many models that use passive keyless entry and start can be targeted with relay techniques. Some manufacturers now include motion-sensing key fobs, better cryptography, or additional checks to reduce the risk, but there are still plenty of vehicles on the road that will unlock and start if they “see” a valid key signal, no questions asked.
Think of it as a spectrum: some vehicles are wide open to simple relays, some are much harder to abuse, and many sit somewhere in between. The safest assumption is that if your vehicle unlocks itself when the key is nearby, you should treat relay attacks as a realistic threat and layer in extra controls.
Yes, if they are built well and in good condition, Faraday pouches and boxes can dramatically reduce the risk of a relay attack because they prevent the key’s radio signal from escaping. The issue is not whether the concept works; it is whether a particular product maintains its blocking performance over time.
Low-quality or heavily worn pouches can develop gaps, seams, or thin spots that let enough signal leak out for attackers to capture. The simplest test is to put your key in the pouch, walk up to the car, and see if it still unlocks. If it does, that pouch has effectively failed and should be replaced.
Unfortunately, yes. Relay attacks are not the only way to steal a vehicle; they are just one of the quieter and more convenient methods for attackers when keyless systems are available. Criminals may still use more traditional techniques such as breaking into the vehicle to access the OBD port, reprogramming keys, towing, or targeting weaknesses in the alarm or immobilizer systems.
That is why relay defense should be seen as one layer in a broader security strategy. Blocking key fob relays is important, but visible physical deterrents, secure parking, and good asset management practices all still matter. The goal is to remove the easiest options and force the attacker to work harder, longer, and with more risk.
A Faraday pouch is a strong first step, but it should not be the only step. Relying on a single control means you are betting everything on one thing never failing, being lost, or being misused.
Layering defenses is more resilient: keep keys deeper inside the building, use a Faraday pouch or box, enable any available vehicle-side protections, and add a visible physical deterrent like a steering wheel lock. Each layer compensates for the others and makes it much less likely that a single mistake will lead to a loss.
When a company vehicle goes missing, it is important to assume that any devices and documents inside may be compromised. That might mean remotely wiping laptops and phones, revoking VPN tokens, rotating passwords, and reviewing what customer or internal information could have been exposed. Treating vehicle theft as part of your security response, not just a logistics problem, significantly reduces downstream risk.
In most cases, comprehensive auto insurance covers theft regardless of whether the attacker used a relay device, a broken window, or a tow truck. The catch is in the details: policy limits, deductibles, exclusions, and how quickly claims are processed can vary.
For business owners, there is also the gap between what insurance pays and what downtime costs. Even if the vehicle itself is covered, lost work, disrupted projects, and the time required to replace equipment and re-secure accounts can still hit the bottom line. That is why prevention and response planning are both important.
The most reliable source is the owner’s manual or the manufacturer’s support information. Many modern vehicles hide advanced settings behind menu options or mobile apps that owners never explore.
Look for terms like “PIN-to-Drive,” “driver authentication,” “security code,” “immobilizer,” or “keyless entry settings” in the manual or infotainment menus. If you work with a dealer or fleet manager, ask directly whether your specific model supports additional security features and how to enable them. Small configuration changes can make a big difference.