When a data breach hits your client's business, the first call usually goes to their IT team. The second call, if they're lucky, goes to their attorney. At Argus, we work at the intersection of those two calls, and we've seen firsthand what happens when organizations treat a breach as a purely technical event. The legal fallout can last years after the systems are back online.
Here's what every attorney advising businesses needs to understand: the most damaging consequences of a data breach rarely come from the intrusion itself. They come from being legally unprepared to respond to it.
The Breach Is Just the Opening Event
A company can restore its systems within days and still face years of regulatory scrutiny, class actions, contractual disputes, and reputational damage. The legal clock starts ticking the moment a breach is discovered; and in many cases, before an organization even knows what happened.
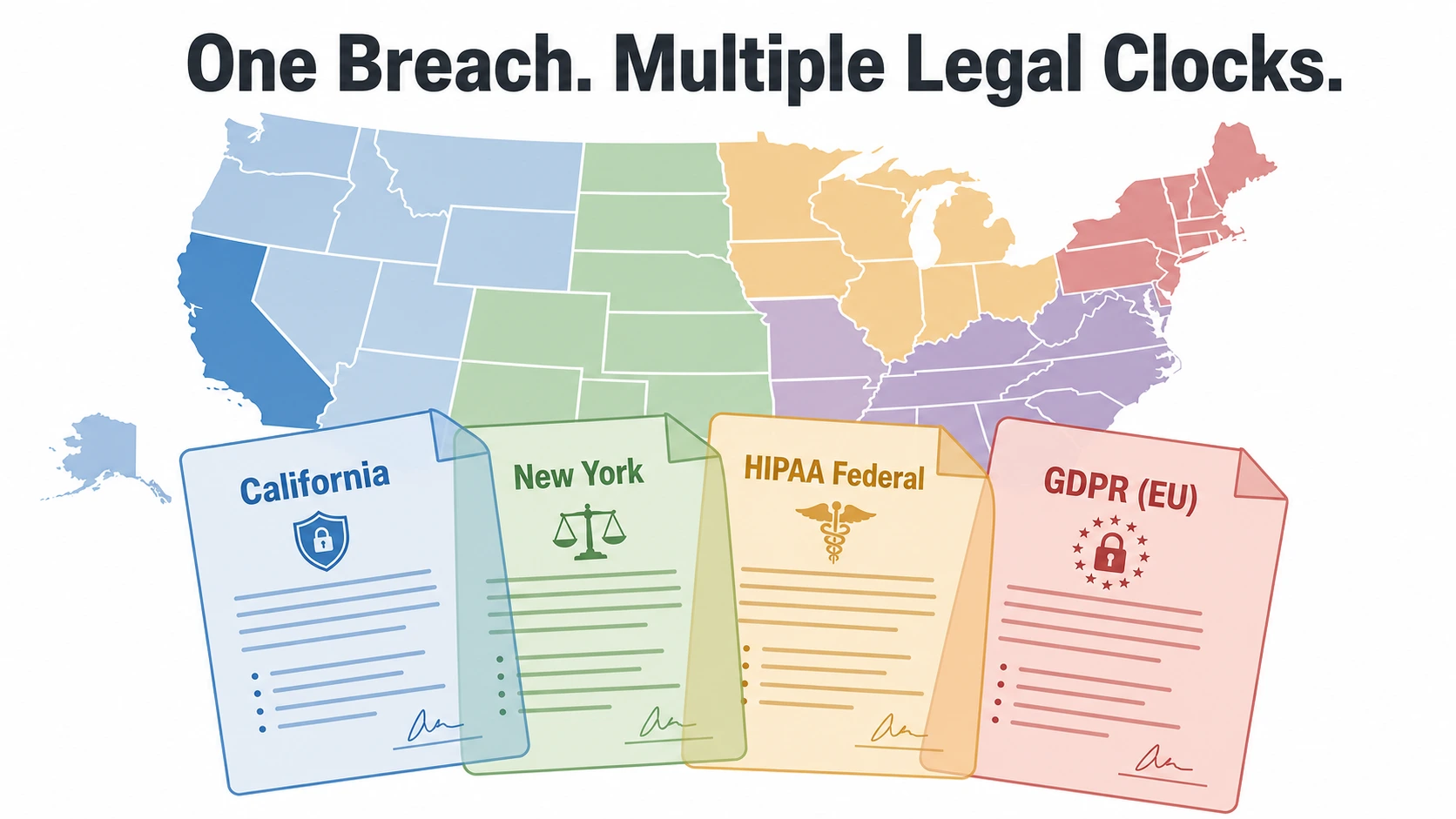
The problem is structural. U.S. breach law is fragmented across fifty state statutes, sector-specific federal rules (HIPAA, Gramm-Leach-Bliley, SEC cybersecurity disclosure), and international frameworks like the GDPR. These laws don't agree on what a "breach" even is. Some require unauthorized acquisition of data. Others trigger on unauthorized access alone, even when exfiltration can't yet be confirmed. That distinction can determine whether your client must notify customers, regulators, insurers, or business partners. All while the investigation is still underway.
This is the legal definition problem. And it's one organizations have to solve in real time, under pressure, with incomplete facts.
The Technical Cause Becomes Legal Evidence
Attorneys often focus on the notification and response side of a breach. But the cause of the breach matters just as much, and often earlier.
Courts and regulators don't simply ask whether an organization was victimized. They ask whether the organization acted reasonably given foreseeable risk. A phishing attack becomes evidence of inadequate training and authentication controls. An unpatched vulnerability becomes evidence of poor patch management. A misconfigured cloud environment becomes evidence of inadequate oversight. In FTC v. Wyndham Worldwide Corp., the Third Circuit confirmed that the FTC can pursue organizations for unreasonable data security practices under its Section 5 unfairness authority. Well before any specific statutory breach definition is implicated.
The Equifax litigation made the same point from the plaintiff's side. Negligence claims advanced, in part, on allegations that the company failed to patch a known vulnerability. The lesson: breach causation becomes part of the legal narrative your client will have to defend. If the root cause looks preventable, the legal position becomes significantly harder.
Vendor and supply-chain breaches add another layer. When a third-party provider is compromised, organizations often argue the breach was "someone else's fault." Regulators and courts have largely rejected that framing. The question isn't where the failure originated; it's whether the organization exercised meaningful oversight and had a plan for third-party incidents.
Notification: Speed vs. Accuracy
Breach notification law is designed to protect consumers, but it creates a serious operational tension for responding organizations. Statutes demand rapid notice, while accurate and legally defensible notice requires careful investigation.
California requires notification "in the most expedient time possible and without unreasonable delay." New York imposes similar requirements and adds regulatory reporting in certain circumstances. HIPAA has its own notice timeline and reporting obligations to HHS. Public companies face SEC cybersecurity disclosure requirements. Organizations handling EU resident data may be subject to GDPR's 72-hour supervisory authority notification rule.
The consequence of rushing: organizations are often making legal representations while key facts are still uncertain. If a customer notice, a regulatory filing, a press release, and an investor statement all go out within a short window, and any of them conflict, omit material information, or overstate certainty, they can each become an independent source of liability. The SEC's enforcement action against SolarWinds demonstrates that how an organization talks about its cybersecurity posture and an incident can itself become the basis for enforcement.
Why Insurance and Contracts Aren't Enough
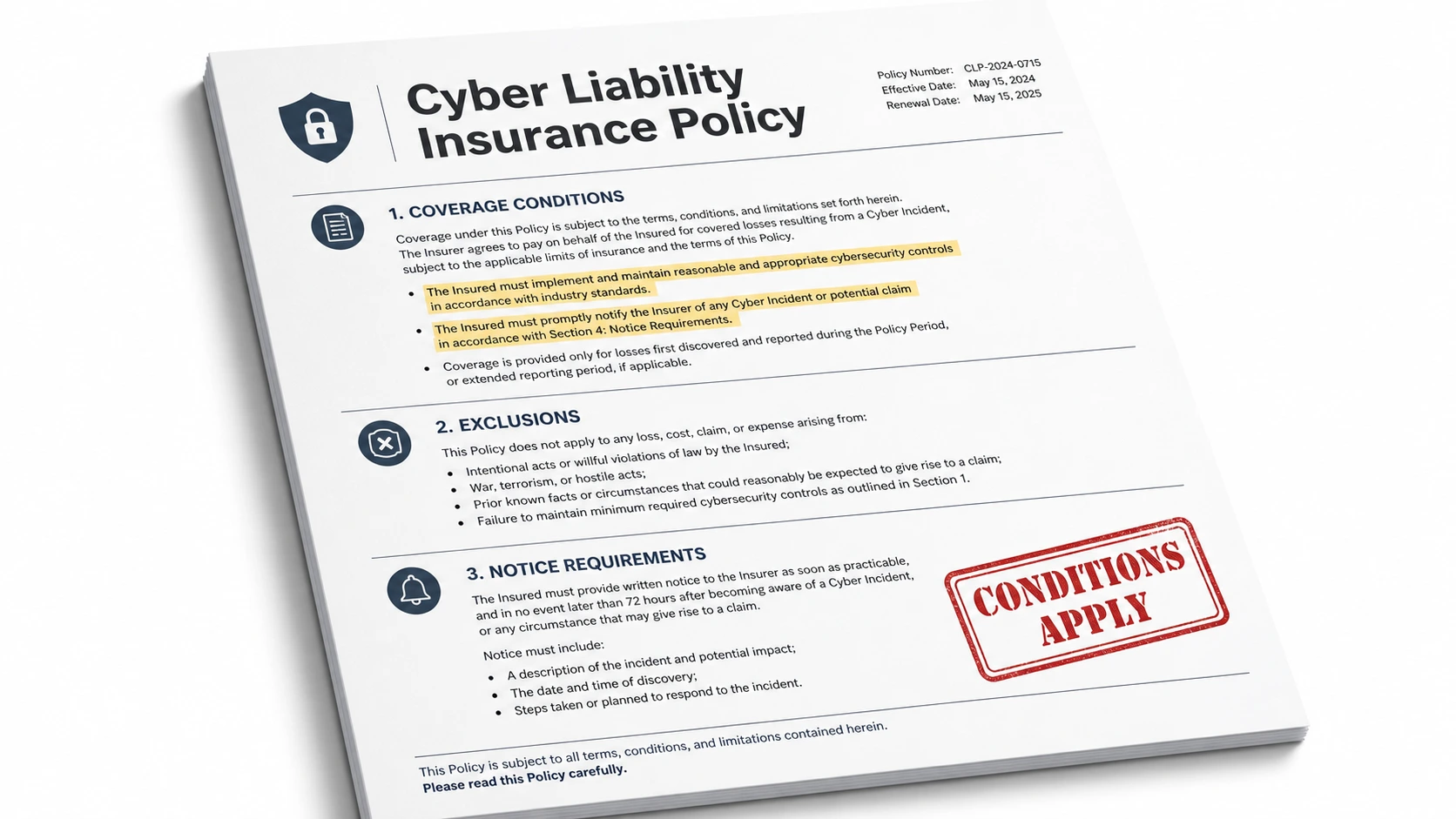
Most businesses and their attorneys know they have cyber insurance. Many assume it will cover the damage. It often doesn't fully. Understanding why matters.
Cyber policies typically cover forensics, legal counsel, notification, business interruption, and sometimes ransomware costs. But coverage is conditioned on timely insurer notice, the use of approved vendors, accurate underwriting representations, and the maintenance of specified security controls. When an insurer disputes whether those conditions were met, the coverage the organization was counting on may be reduced or denied entirely. Merck v. ACE American Insurance Co. illustrates how coverage disputes can escalate to appellate litigation, even on questions as fundamental as whether a policy exclusion applies at all.
Contracts carry similar limitations. Indemnification clauses, liability caps, and data processing agreements may shift some financial risk; but they don't prevent regulators from holding your client accountable for its own conduct, and they don't guarantee reimbursement when contract language is ambiguous or competing agreements conflict.
The Governance Gap
One of the most consistent findings in post-breach litigation and regulatory enforcement is this: organizations fail not because they lacked technology, but because they lacked a decision-making structure when it mattered most.
During an active breach, the following questions need immediate answers:
Who has authority to declare an incident?
Who retains outside counsel?
Who engages the forensic vendor?
Who notifies the insurer?
Who approves external communications?
Who determines whether a legal reporting threshold has been met?
Without a preexisting incident response plan that assigns those roles and decisions, the response becomes disorganized, and disorganization creates liability. ABA Formal Opinion 483 recognizes this directly. Attorneys have professional obligations after a cyberattack affecting client data, including communication duties that may arise even when the lawyer's ability to provide services was materially impaired. The same governance principle applies to every organization the attorney advises.
What Legal Preparedness Actually Looks Like
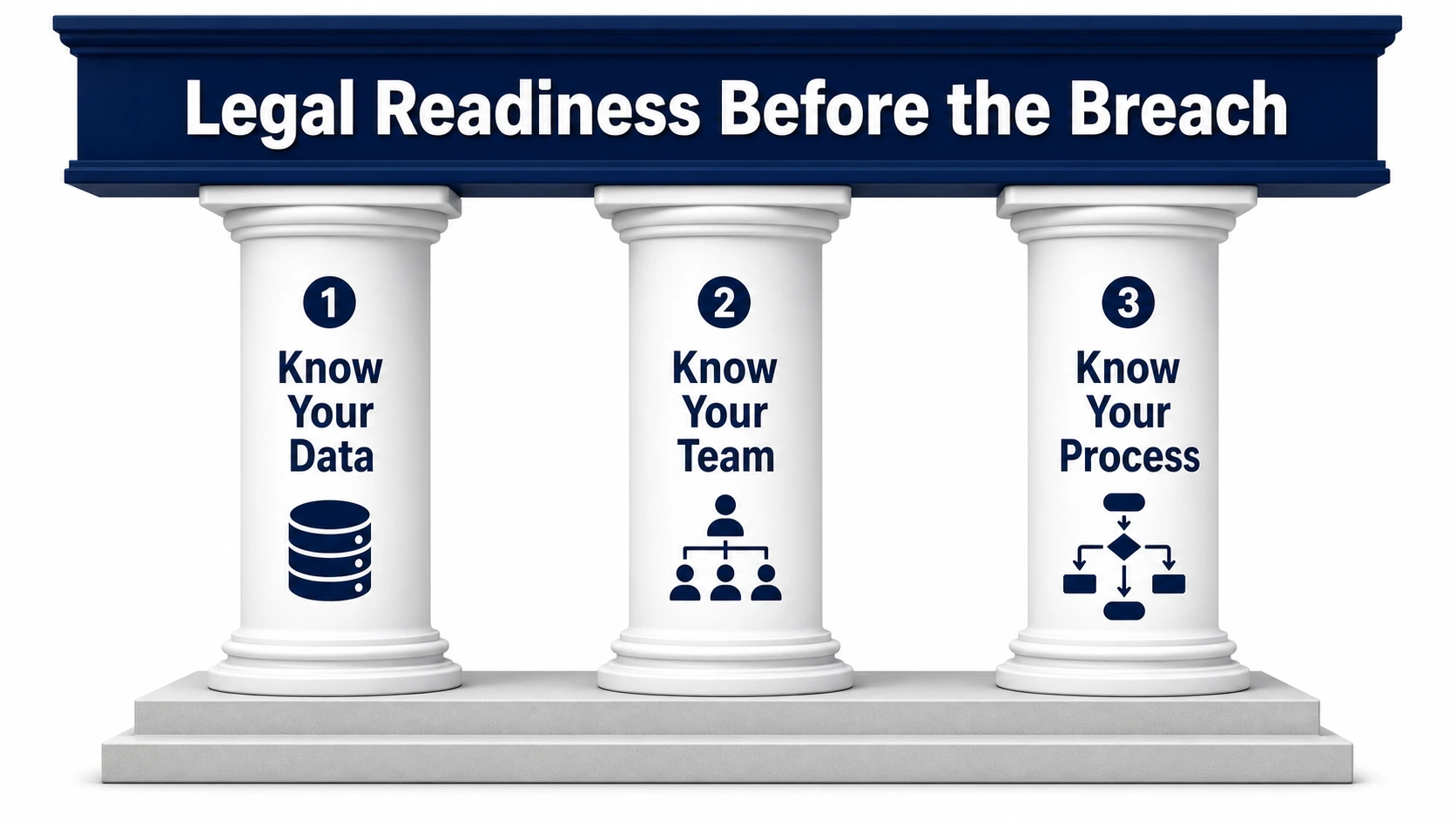
The organizations that fare best in breach-related litigation and enforcement are the ones that did the hard work before the breach happened. That work comes down to three things:
- Know your data. Maintain a current inventory of what sensitive information exists, where it is stored, how long it is retained, and which vendors have access to it. You cannot classify an incident correctly, or notify the right parties, if you don't know what data was in scope.
- Know your team. A cross-functional incident response group (including legal counsel, technical responders, executive leadership, communications personnel, and insurance and vendor coordinators) should be identified and empowered before any crisis begins.
- Know your process. Documented and tested playbooks, realistic tabletop exercises, clear evidence-preservation procedures, and an understanding of every contract and policy notice trigger. These aren't just best practices. They are the evidence of reasonableness that regulators and courts examine when evaluating organizational conduct after a breach.
The Bottom Line for Law Firms
If you advise businesses, particularly those in regulated industries, professional services, or any organization that handles personal data, your clients face meaningful legal exposure the moment a breach occurs. Whether they come through that exposure with defensible outcomes depends substantially on the work they did before it happened.
At Argus, we help organizations build that legal readiness on the technical side. We work with internal teams and outside counsel to ensure that when an incident occurs, the evidence trail, the response structure, and the security documentation are all in order, so your client isn't improvising legal decisions in the middle of a crisis.
A breach is a legal event from the first moment.
We help make sure your clients are ready for it.